Documentation Index
Fetch the complete documentation index at: https://docs.allquiet.app/llms.txt
Use this file to discover all available pages before exploring further.
OpenID Connect (OIDC) and SCIM are available on Pro & Enterprise plan only.
OpenID Connect (OIDC)
This integration allows your organization to utilize its existing identity provider (IdP) services to manage user access to All Quiet.Step-by-Step-Guide
For this process, you need access SSO tab of your organization, only accessible to users with Organization Owner role.
Create an Organization
To use OIDC, you first need to create an Organization in All Quiet. If you also want to use SCIM to provision your users, please note that the user (“root user”) who creates the Organization cannot be provisioned through SCIM. We recommend to create the Organization with a “root user” that is not bound to a specific employee, like devops@yourcompany.com.
Setting up in Your IdP
In your identity provider’s management console, you will need to register All Quiet as a new application and give your users access to it.In your IdP’s application, you will need to configure the following:Configure the Redirect URI in your IdP:
Make sure to create an application that uses OIDC, not SAML, as the authentication type. Also, if you want to add SCIM provisioning, make sure the application supports SCIM provisioning as well.
https://allquiet.app/signin-oidc(US Hosted) orhttps://allquiet.eu/signin-oidc(EU Hosted).
https://allquiet.app/login(US Hosted) orhttps://allquiet.eu/login(EU Hosted).
OIDC with Microsoft Entra ID
In your OIDC tenant’sAPI Permissions settings, add email, offline_access, openid and profile permissions.
Mark all these permissions as type Delegated and without requiring Admin consent.Also, in the Token Configuration, add email claims.Authority URL (important): Microsoft Entra has two OIDC endpoint versions. The Authority URL determines which discovery document and token endpoint are used.- Recommended (v2.0 / Microsoft Identity Platform):
https://login.microsoftonline.com/{tenant-id}/v2.0
Use this for modern OIDC setups and scope-based permissions (likeopenid,profile,email,offline_access). - Legacy (v1.0):
https://login.microsoftonline.com/{tenant-id}
Only use this if you have a legacy setup that explicitly requires v1.0 tokens.
OIDC with Jumpcloud
In your OIDC tenant’sOIDC Single Sign-On Configuration- Select “Client Secret POST” as
Client Authentication Type - Select Standard Scopes “Email” and “Profile”. No need to further adjust the mapping of single attributes.
- The Authority URL can be found here.
OIDC with Google Workspace
You’ll need to additionally configure the Redirect URI:https://allquiet.app/signin-oidc(US Hosted) orhttps://allquiet.eu/signin-oidc(EU Hosted).
https://accounts.google.com.OIDC with Okta
The Authority URL for Okta ishttps://{tenant}.okta.comOIDC with Auth0
The Authority URL for Auth0 ishttps://{tenant}.auth0.com.Set up OIDC Tenant in All Quiet Web App
After setting up the application in your IdP, you need to set up the OIDC tenant in All Quiet Web App.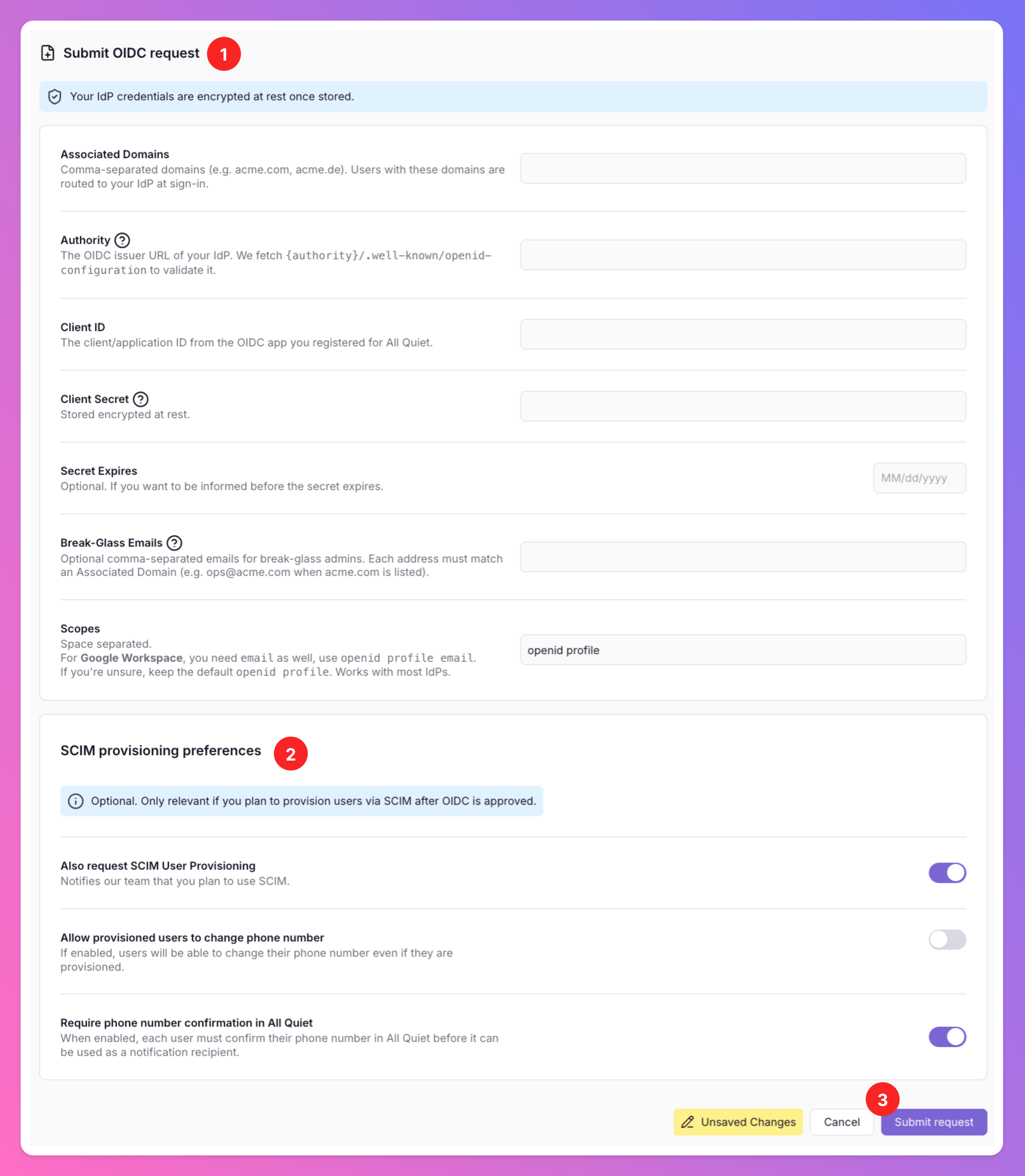
- Go to
Organizations - Select your organization
- Click on
SSOtab - Click on
Submit OIDC requestbutton.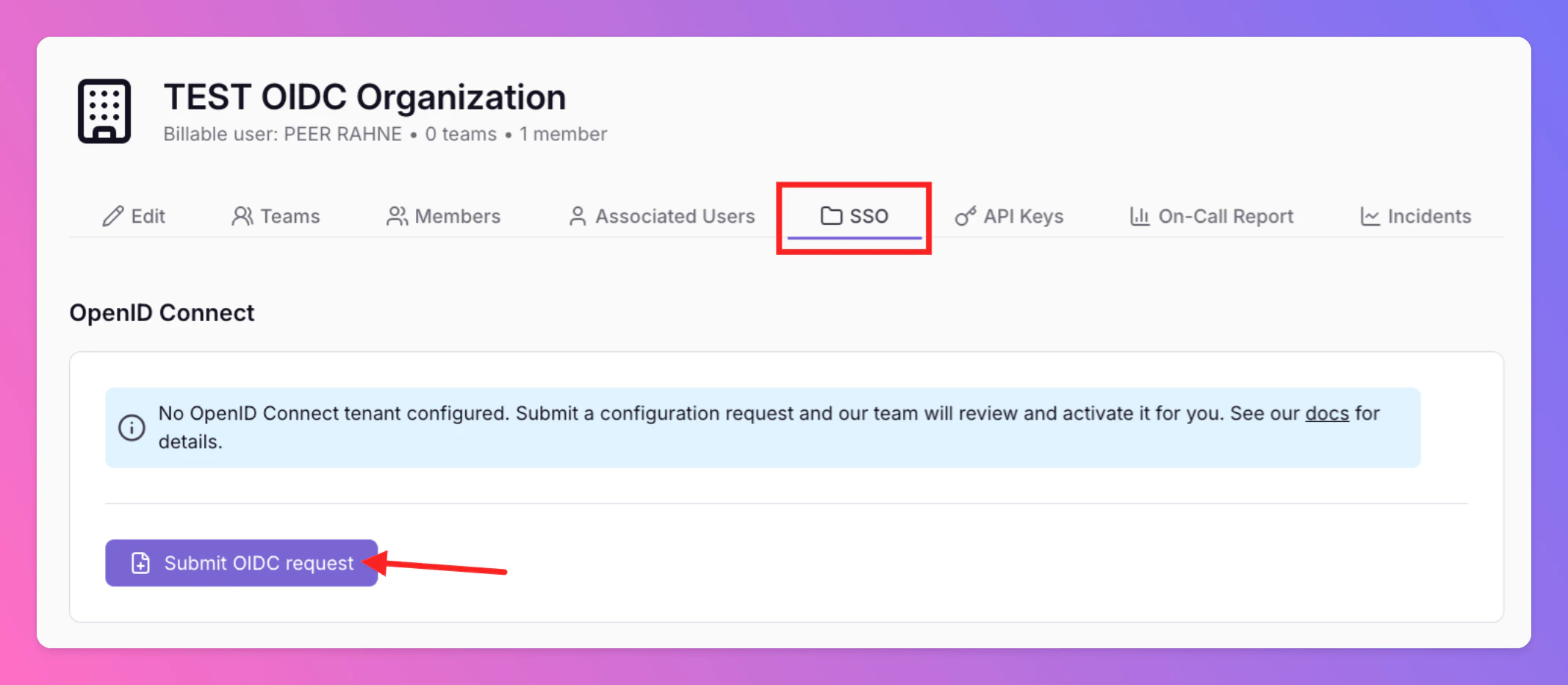
-
Submit OIDC request:
- Associated Domains: Enter the domains you want to associate with the OIDC tenant. Only add domains you control. You can add multiple domains by separating them with a comma. We will validate the domains you add after you submit the request.
- Authority URL: Enter the Authority URL from your IdP’s application that you’ve received in the previous step. We fetch
{authority}/.well-known/openid-configurationto validate it. - Client ID: Enter the Client ID from your IdP’s application that you’ve received in the previous step.
- Client Secret: Enter the Client Secret from your IdP’s application that you’ve received in the previous step. Do not share this secret with anyone. All Quiet will store your IdP credentials securely in our database.
- Secret Expires (optional): Enter the date and time when the client secret will expire. We will remind you 2 weeks before the secret expires.
- Break-Glass Emails (optional): Break-Glass Emails can be used to bypass OIDC sign-in and typically are not tight to a individual person, but rather a service account e.g. admin@acme.com. Each email domain must match an Associated Domain you listed above (subdomains are allowed). Add multiple emails by separating them with a comma.
- Scopes: Space-separated OIDC scopes. The default is
openid profile, which works with most IdPs. For Google Workspace, includeemailas well — useopenid profile email. If you’re unsure, keep the defaultopenid profile.
-
Optional: Set SCIM provisioning preferences:
If you want to set up SCIM provisioning, too, let us know your preferences during this step.
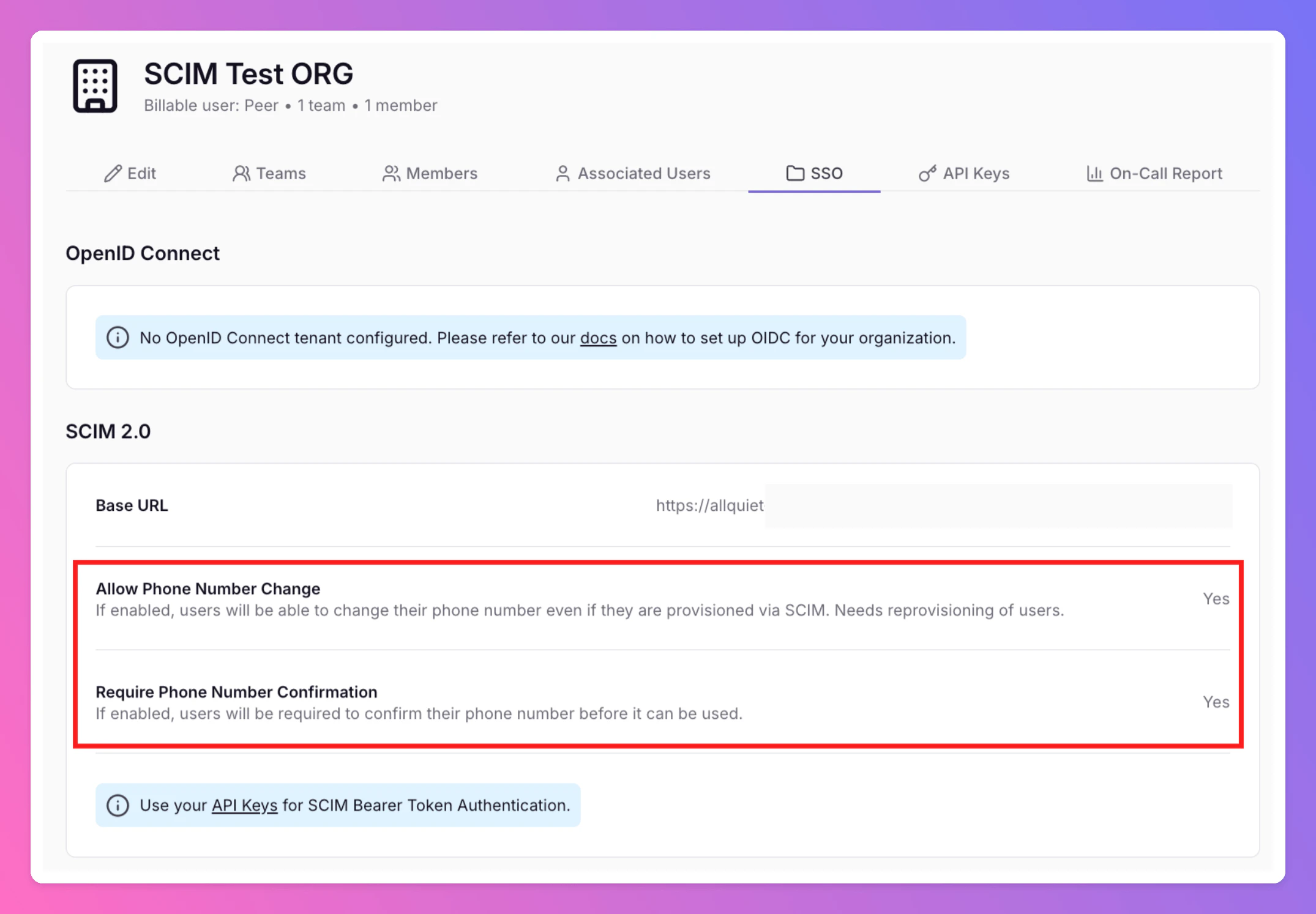
- Define if SCIM provisioned users should be allowed to change their phone number via the Web app.
- Define if SCIM provisioned users need to confirm their phone number via the Web app. We recommend this to be enabled to ensure the phone number is valid and users can receive notifications.
Have you already created users manually and now wish to convert them to SCIM-provisioned users? Let us know the exact users you want to convert after submitting the request by contacting support@allquiet.app.
Submit request button.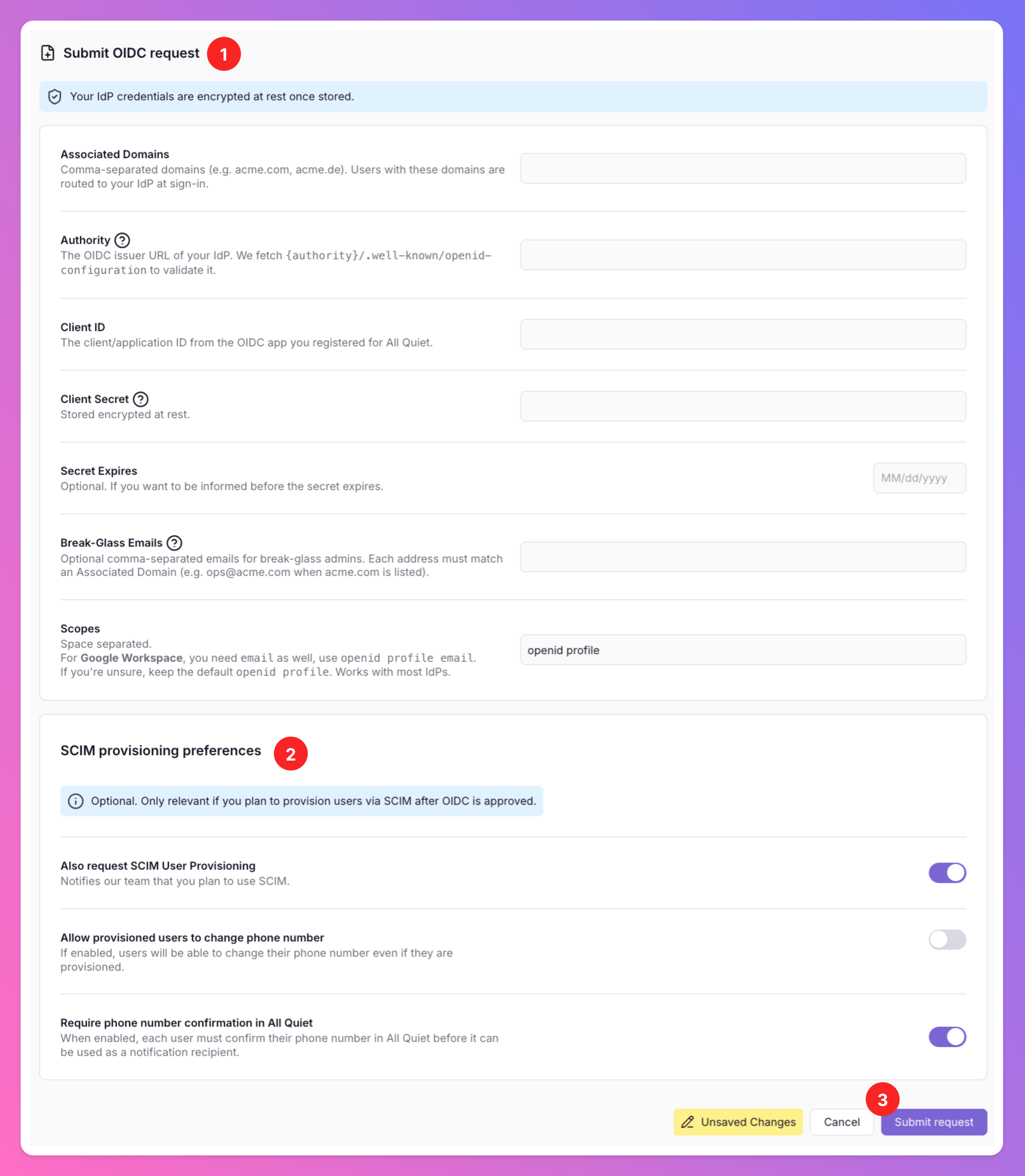
Verification and Activation
After submitting the request, our team will review your request and get back to you if additional information is needed.After successful verification, the integration is considered complete. You will now find your OIDC tenant (and SCIM provisioning preferences if you’ve set them up) in the 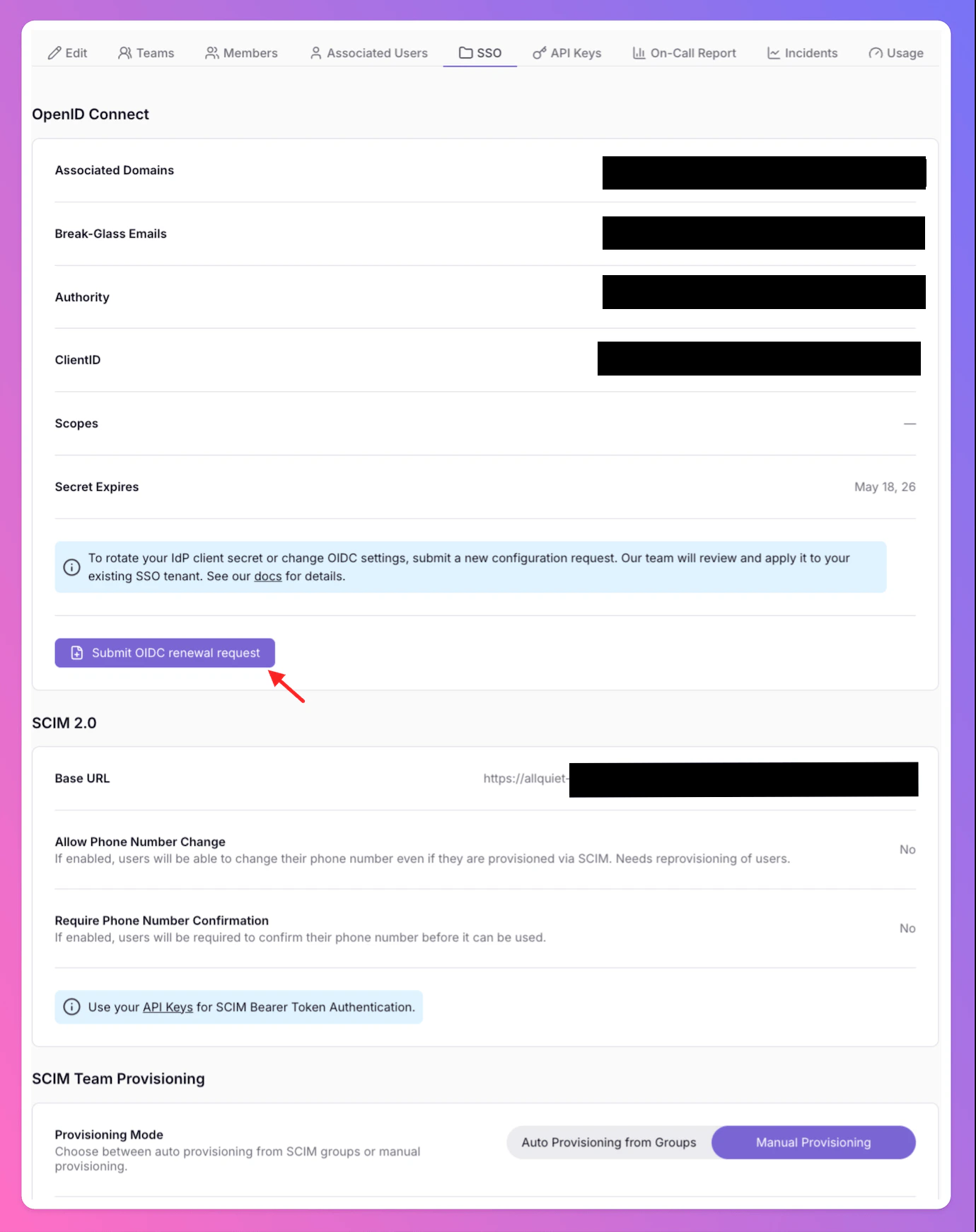
SSO tab of your organization.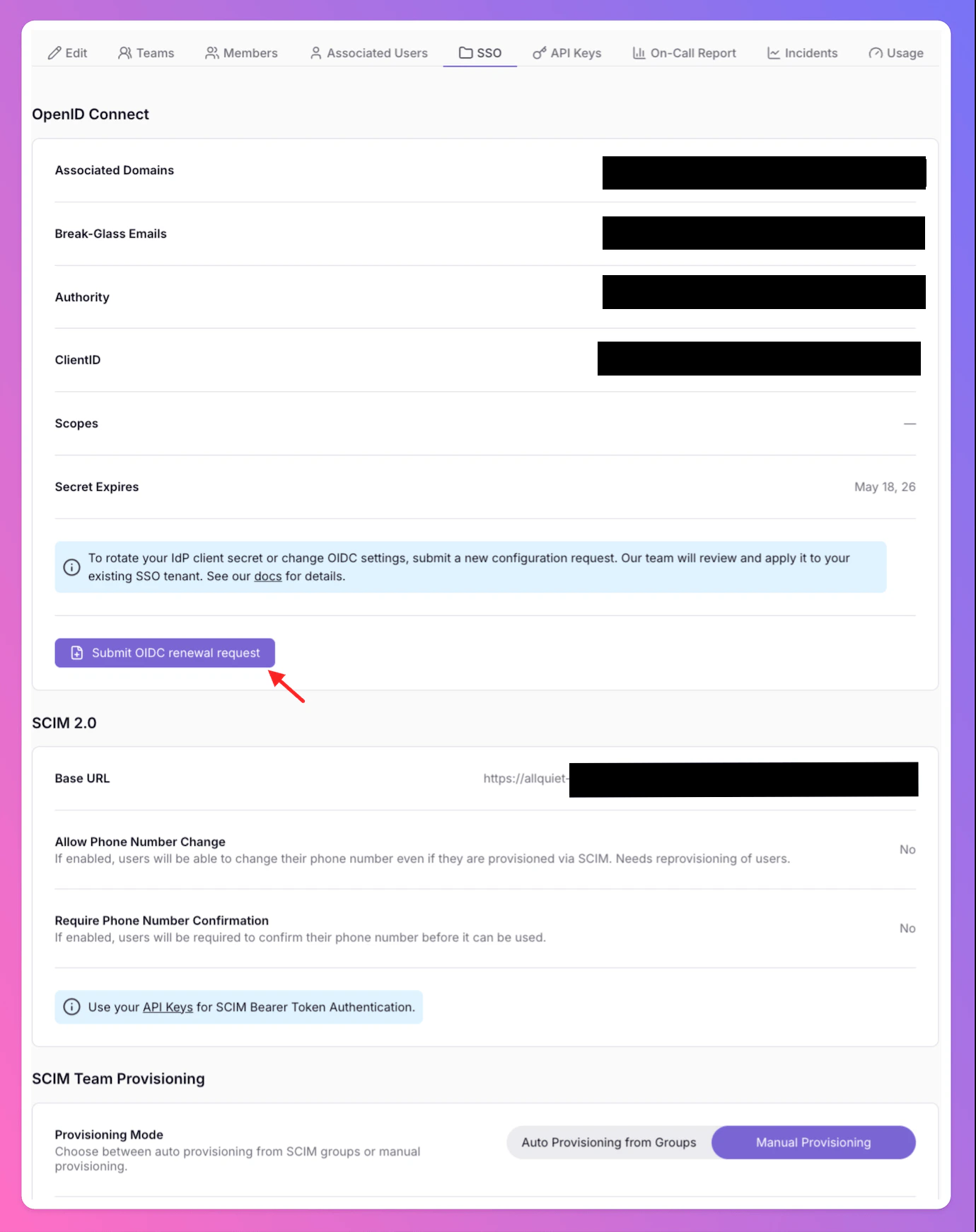
Renewing OIDC credentials
Once your tenant is active, you can use Submit an OIDC renewal request on theSSO tab when you need to rotate your client secret. If your secret is about to expire, we will notify you by email. In the renewal form, provide the new Client Secret and, if applicable, the updated Secret Expires date.Conclusion
Integrating your organization’s SSO using OpenID Connect with All Quiet enhances your platform’s security and user experience. With this setup, you ensure a consistent and secure access management system, aligned with your organizational policies and requirements.SCIM 2.0
Step-by-Step-Guide
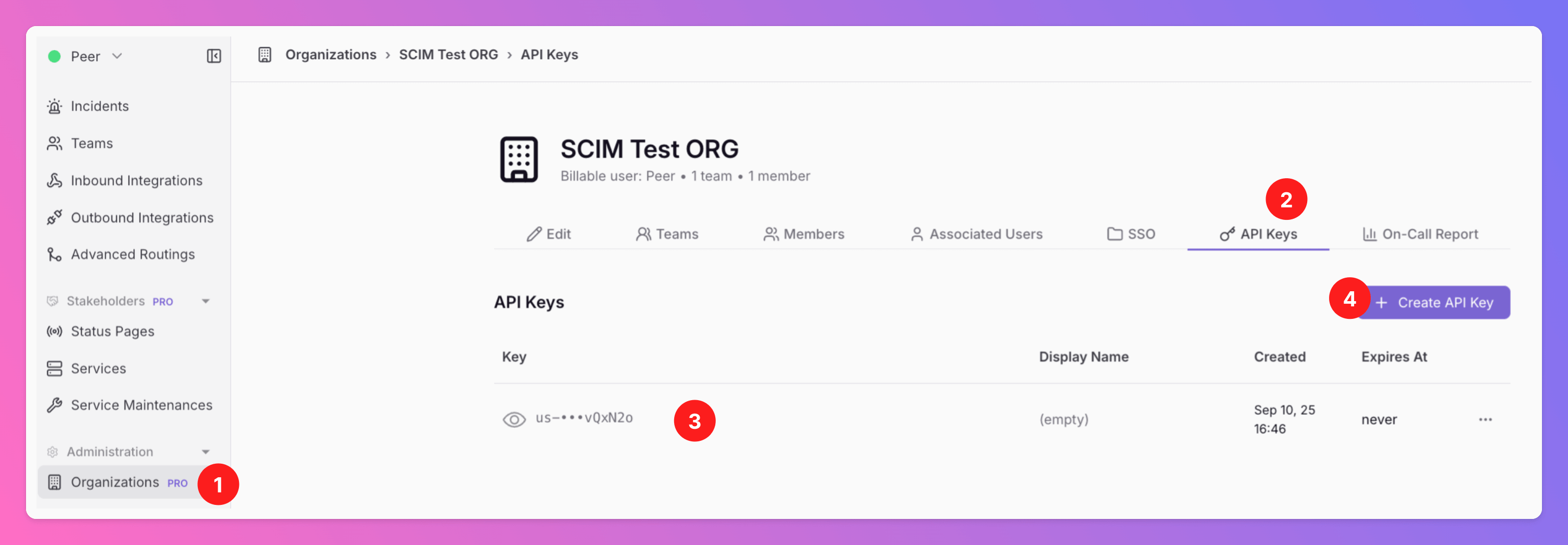
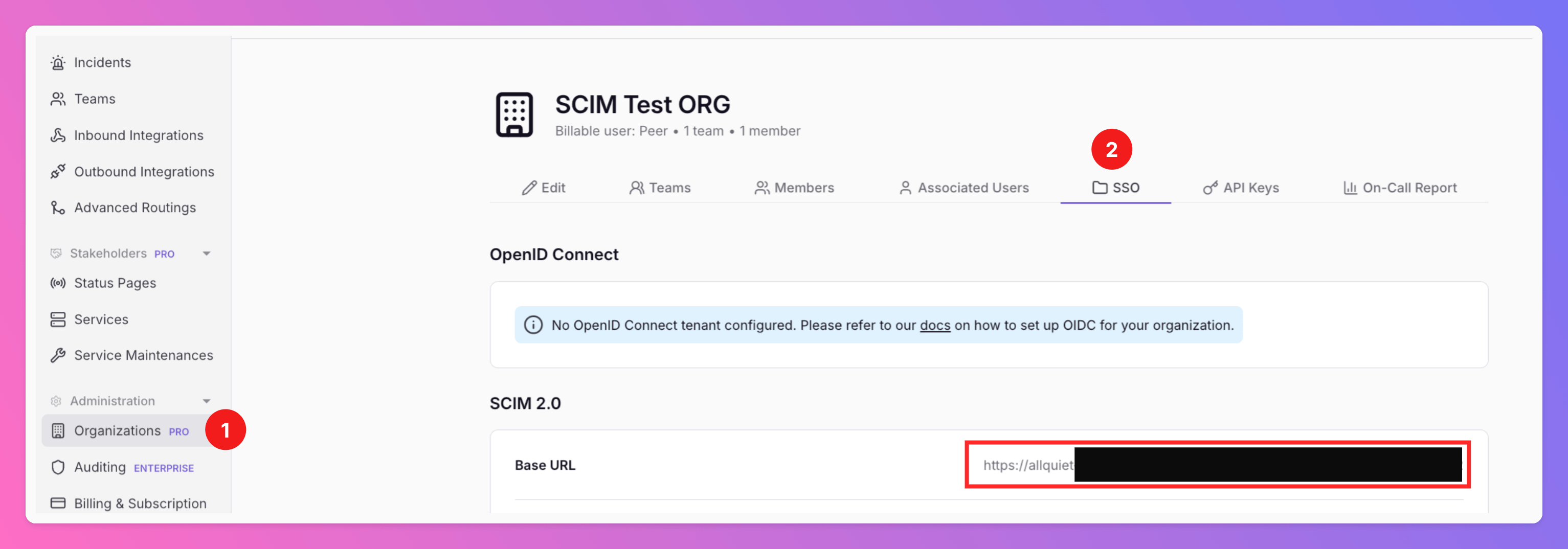
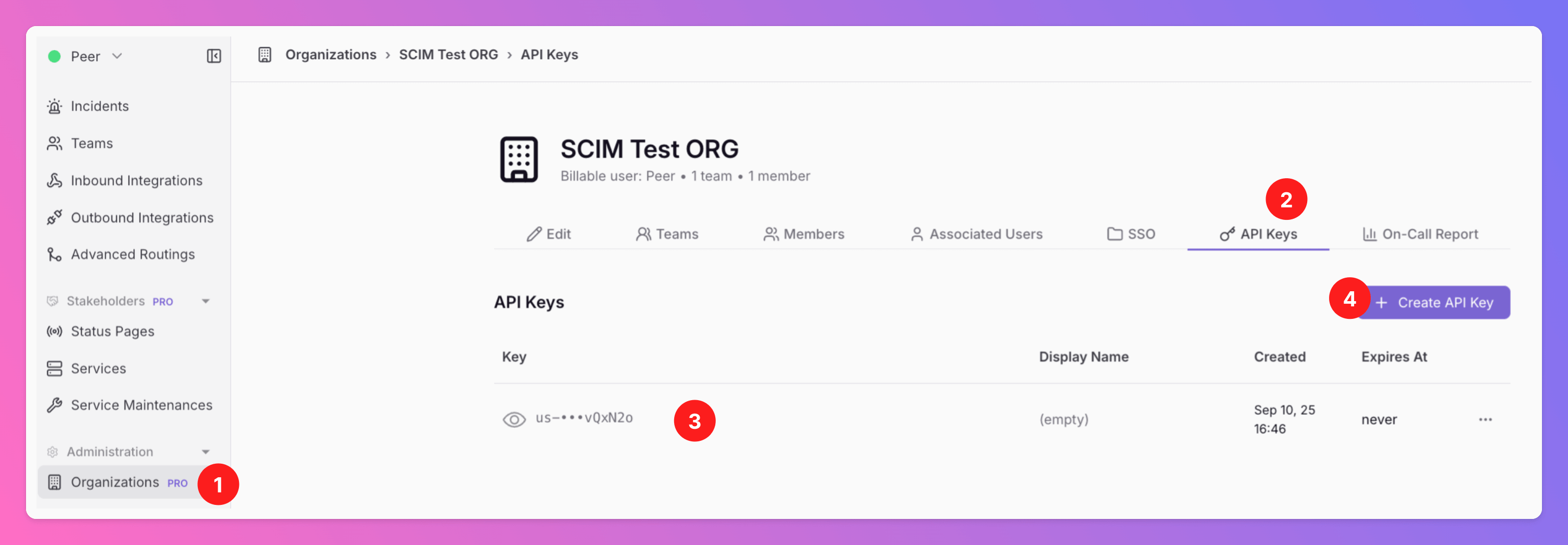
For this process, you need access to the API Keys and SSO tab of your organization, only accessible to users with Organization Owner role.
Create an Organization
To use SCIM, you first need to create an Organization in All Quiet. Please note: The user who creates the Organization cannot be provisioned via SCIM. Therefore, we recommend to create the Organization with a “root user” that is not bound to a specific employee, e.g. devops@yourcompany.com. This way, you ensure all “real” on-call users and employee accounts can be provisioned. If you already set up the Org with your personal account, you can change your account’s email address via the Web app on /app/account to a root user email and later provision your personal email and account via SCIM.
Request OIDC Tenant and SCIM provisioning via All Quiet Web App
OpenID Connect SSO first is a prerequisite for SCIM user provisioning. Follow the OIDC setup guide here and make sure to opt-in for SCIM provisioning.
Have you already created users manually and now wish to convert them to SCIM-provisioned users? Let us know the exact users you want to convert after submitting the request by contacting support@allquiet.app.
If your organizations already has an active OIDC tenant and you want to use it for SCIM provisioning, please contact support@allquiet.app. Please inform us whether SCIM provisioned users should be able to change their phone number and / or confirm their phone number via the Web app.
Retrieve Base URL & API Key
In your SCIM provider’s console, you will need to register All Quiet as a new SSO application.For the integration, you will need to provide the Base URL and API Key of your All Quiet Organization.After approving your OIDC tenant and SCIM provisioning request, our team will create your Organization’s Base URL. It will be visible under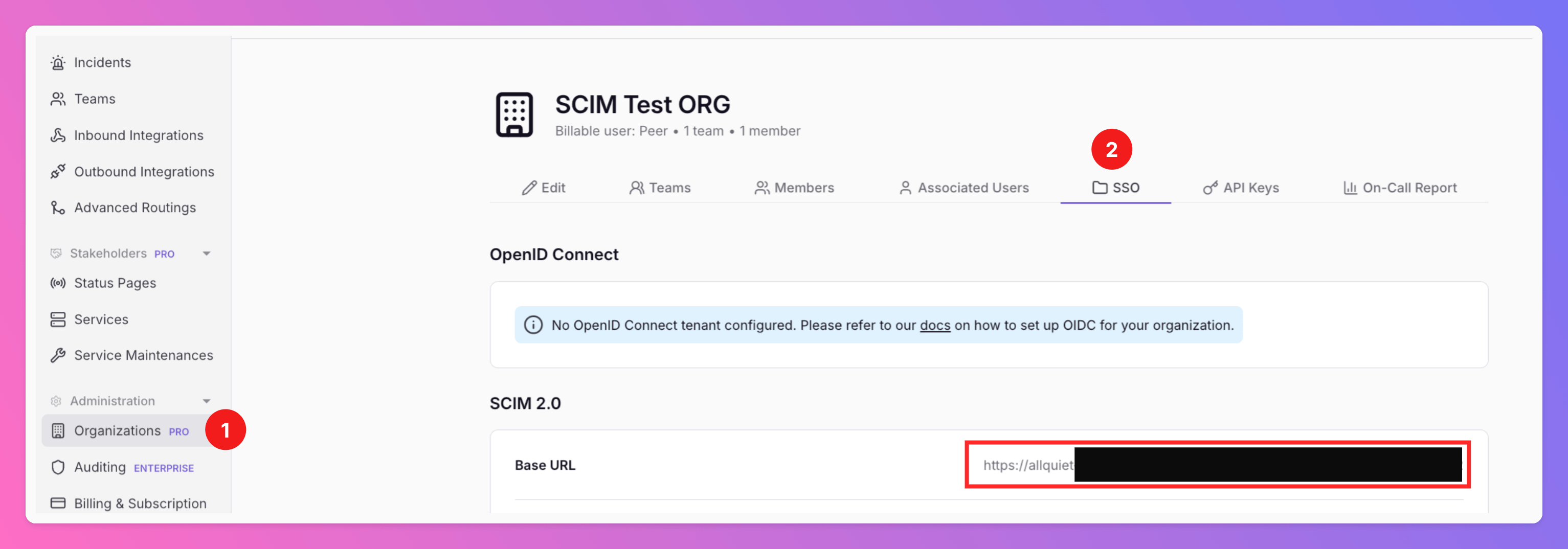
Organizations.- Select your Organization and the tab
SSO.
Organizations.- Select your Organization and the tab
API Keys. - Retrieve your
API Key. - Alternatively, click
+ Create API Keyif you haven’t created one yet.
Verification and Testing
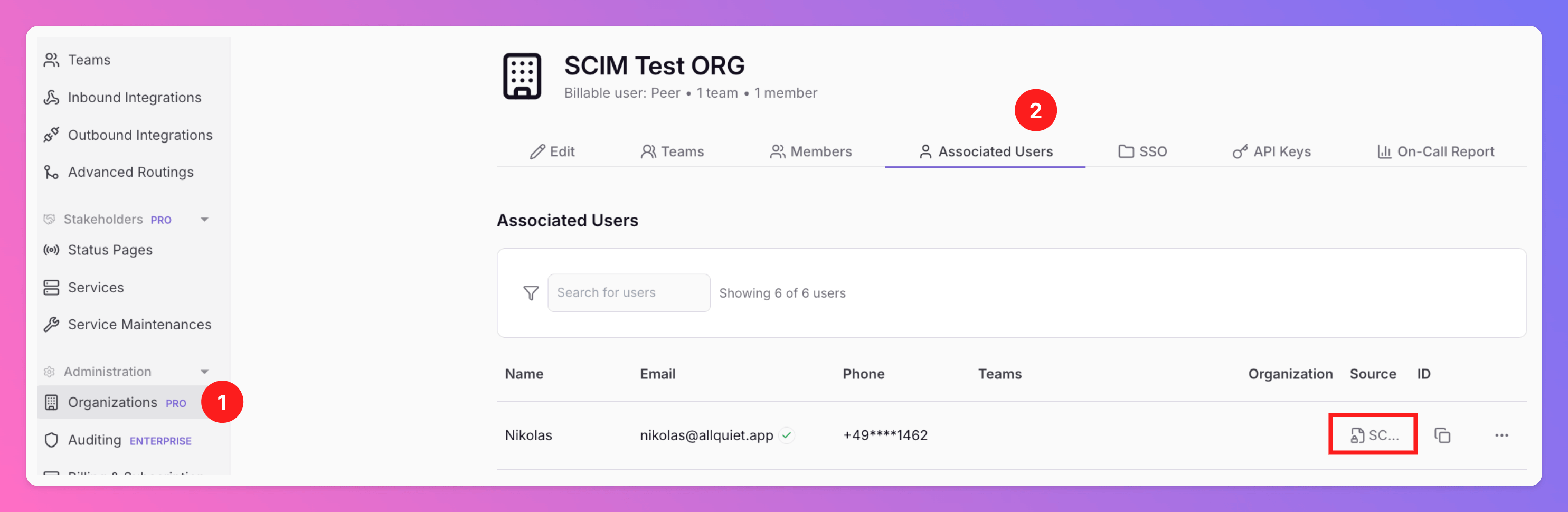
Once the setup is completed, you will find the users provisioned via SCIM under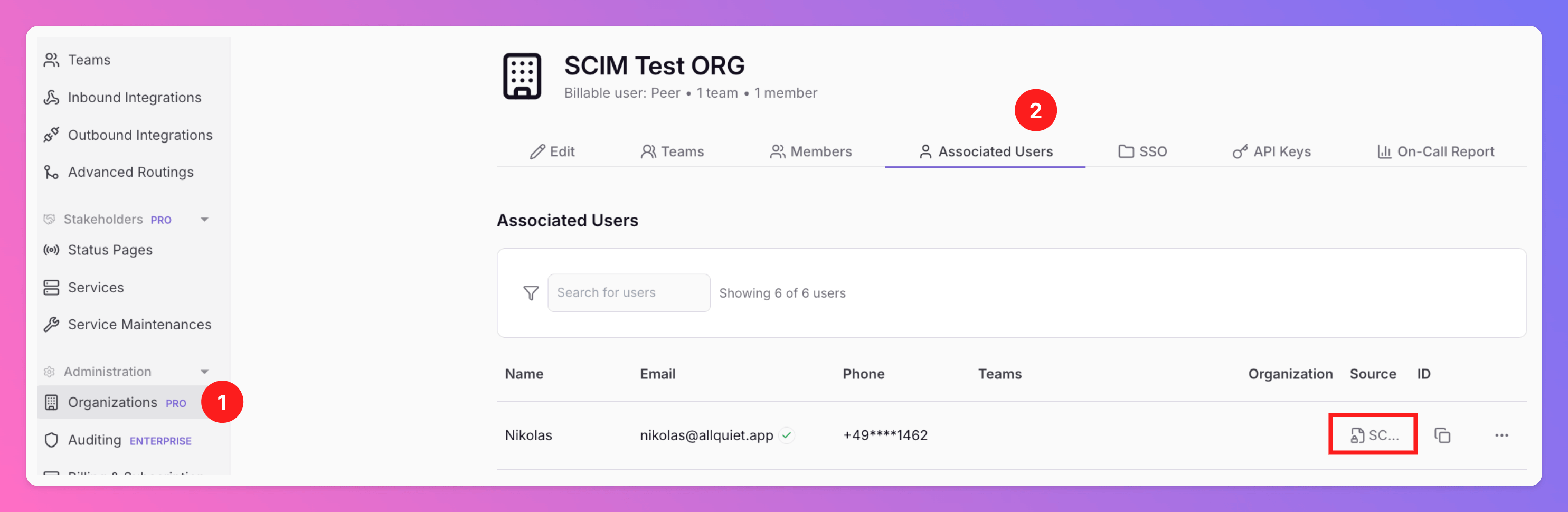
- Organizations
- Tab
Associated Users. TheSourcecolumn will show which users got provisioned via SCIM.
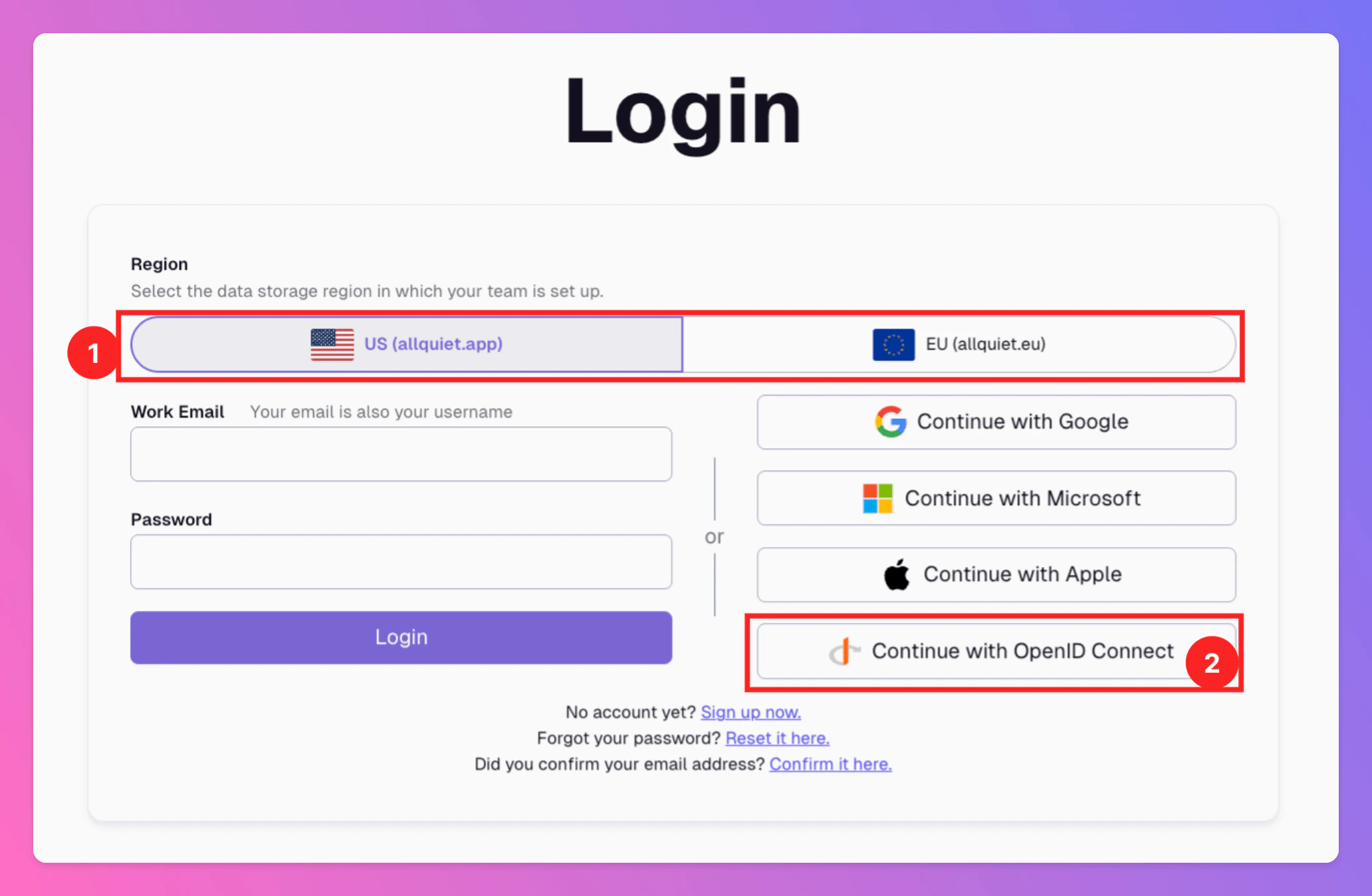
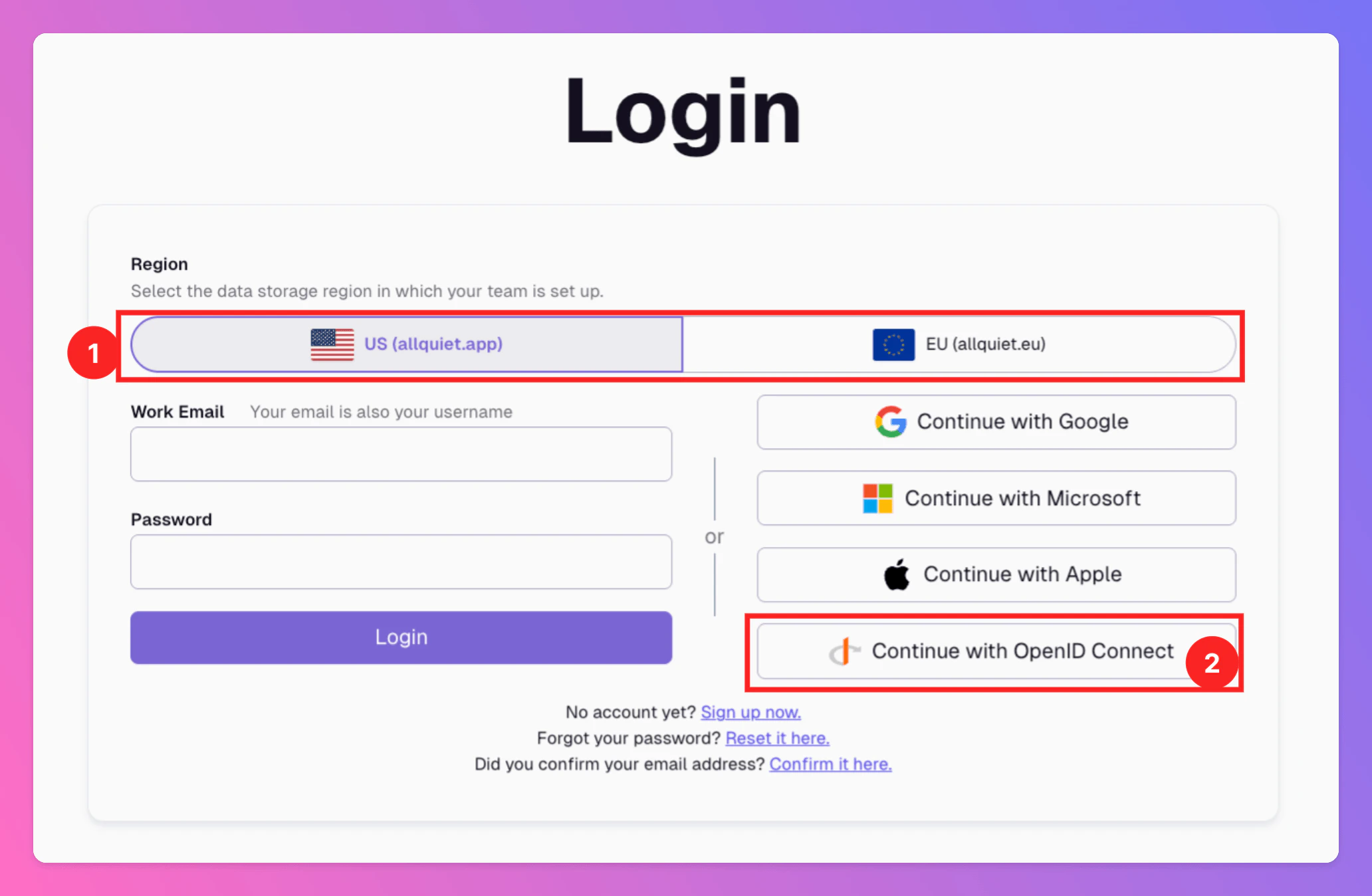
Log in via OIDC
Your SCIM provisioned users can now log in via OIDC. They won’t have a password, so they need to use the OIDC login button to log in.To log in to All Quiet, your users need to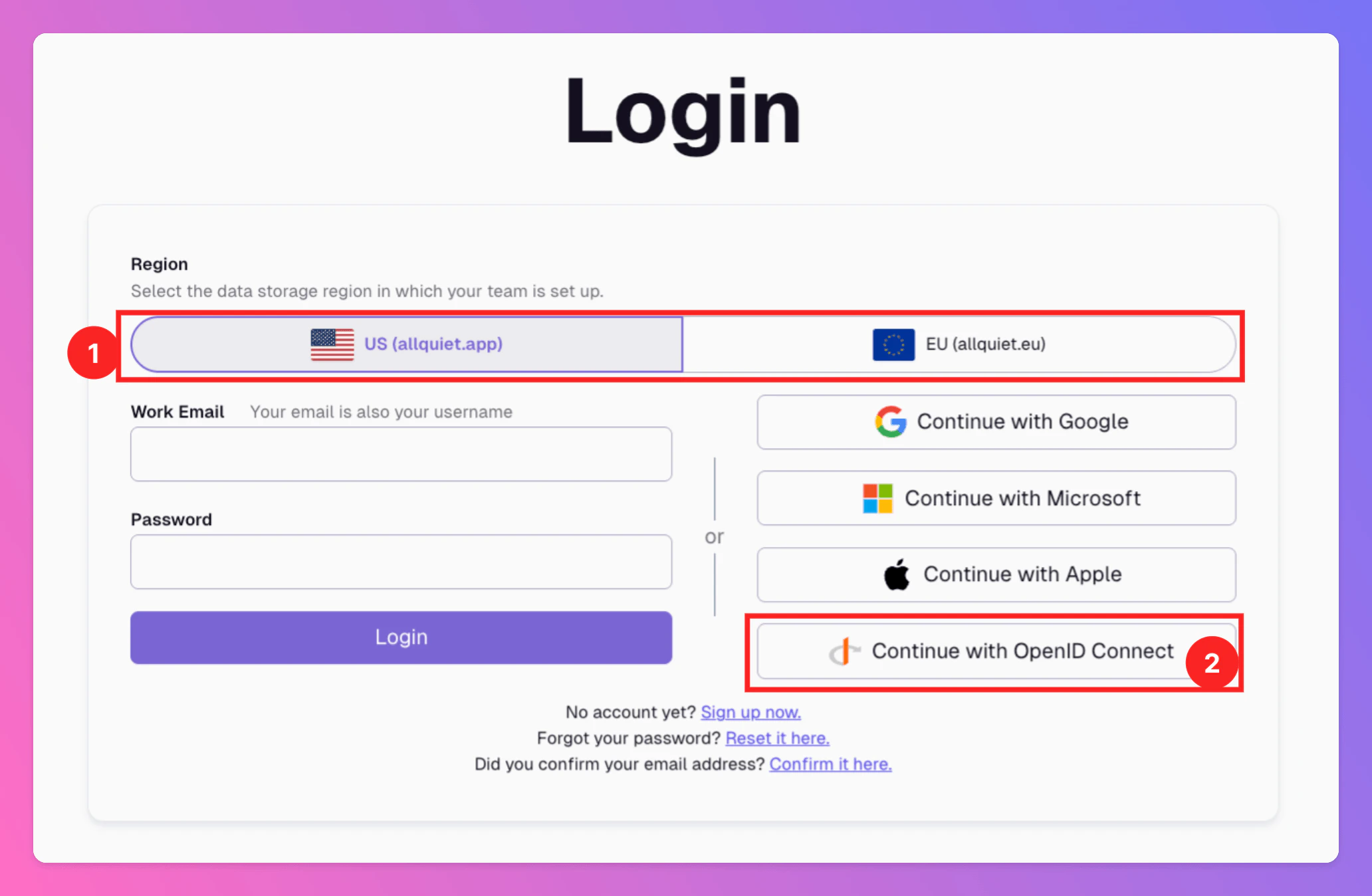
- Select the correct hosting region
- Click on
Continue with OpenID Connect
SCIM Team & Organization Role Provisioning
You can use the User Groups from your SCIM provider for Team & Organization Management in All Quiet. This is a convenient and much leaner alternative to manual team invites for larger organizations.Go to 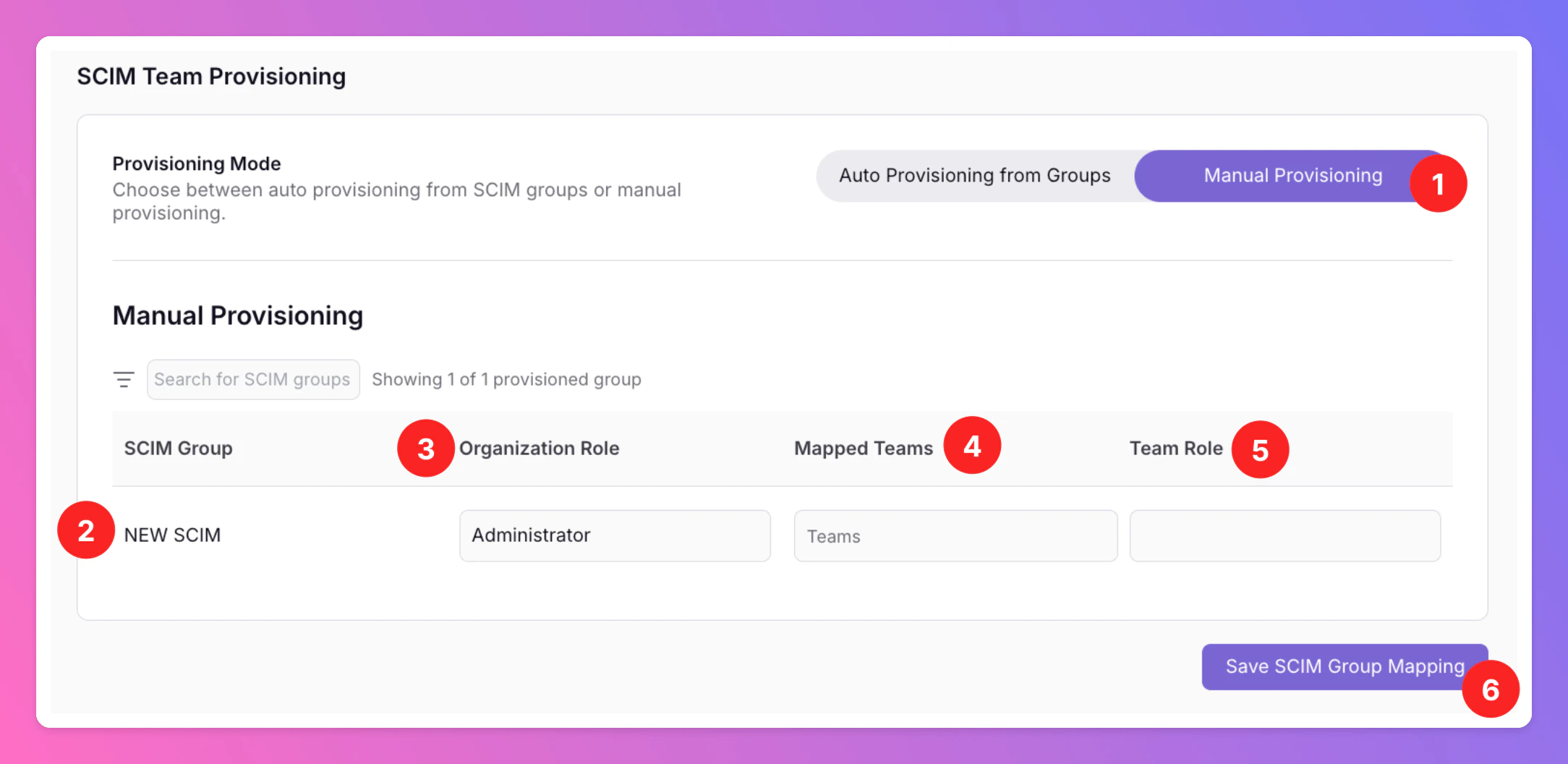
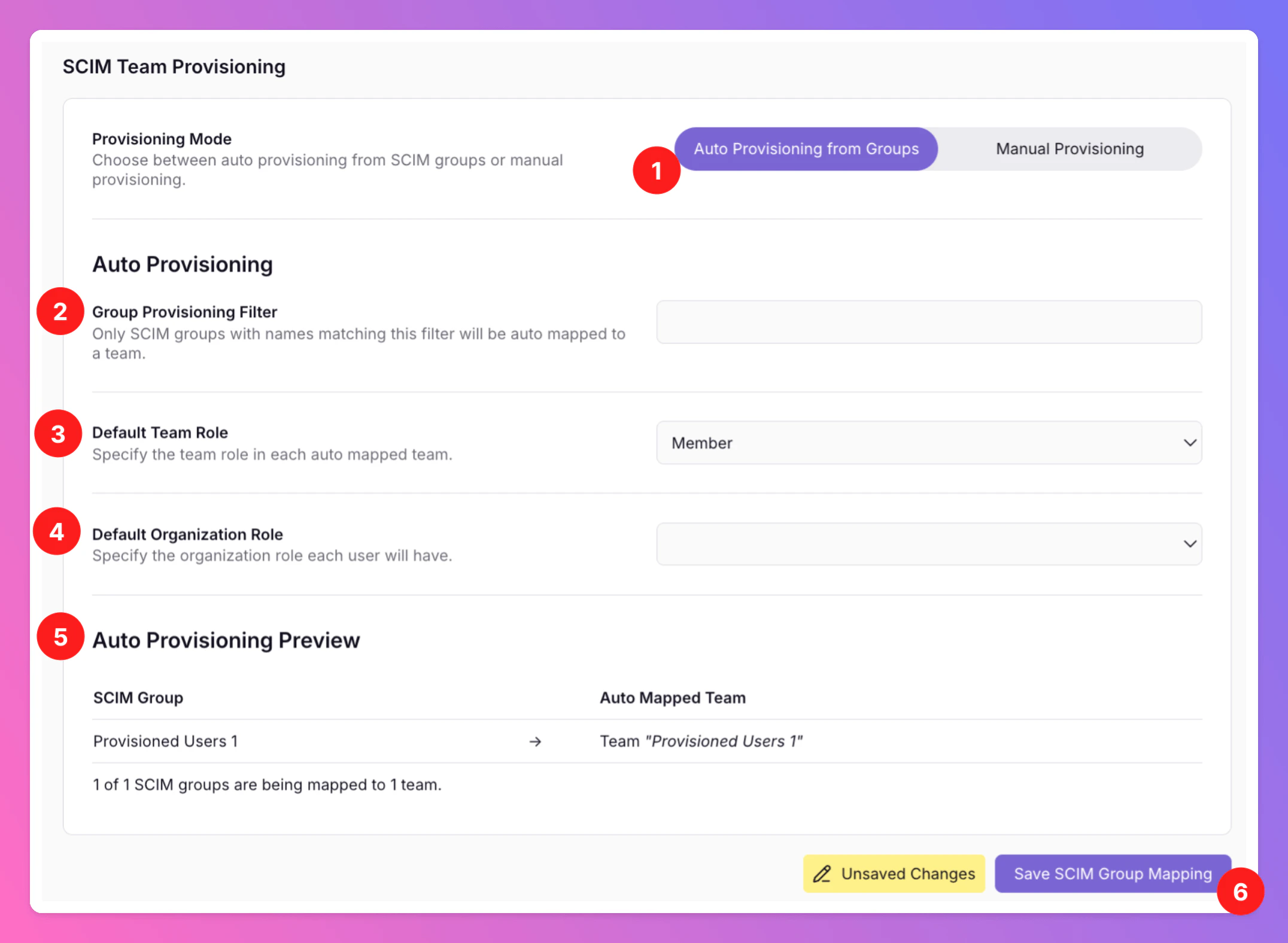
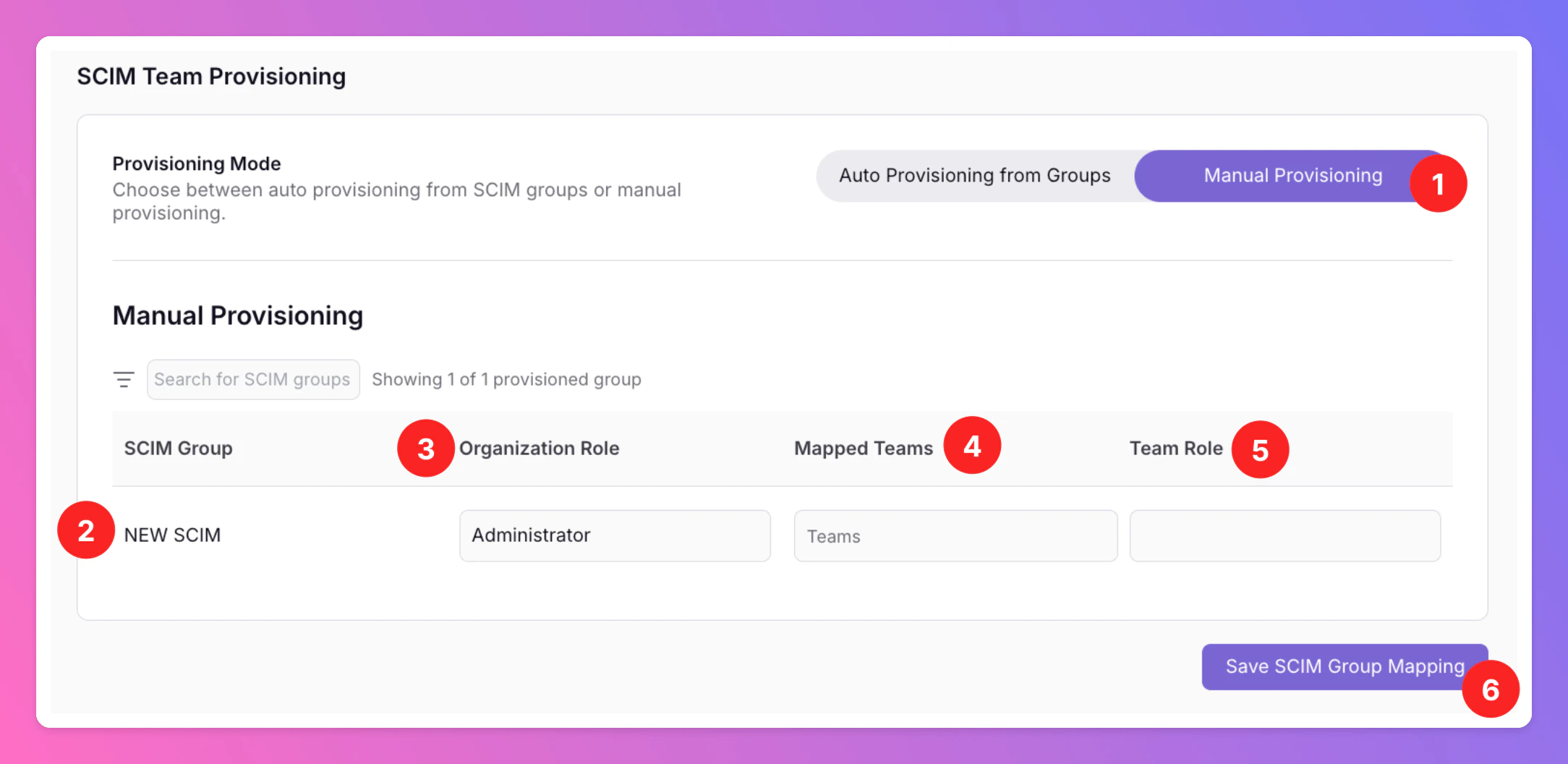
Organizations > SSO.Manual Provisioning Mode- First, you need to select your
Provisioning Mode. We recommendManual Provisioningif you want to be flexible and want to be able to switch SCIM User Groups between All Quiet Teams. - Find your SCIM User Groups below.
- Optionally, you can assign Organization Member, Organization Administrator or Organization Owner roles to the provisioned users.
- Map your SCIM User Groups to All Quiet Teams. For Manual Provisioning Mode, there have to be existing teams for you to be able to map them.
- Choose whether provisioned users should be assigned Member or Administrator roles within the teams. You can update these roles via the Teams section at any time for each User. Learn more about team roles here.
- Save your settings. You will find the Users from your SCIM User Groups in your All Quiet Teams.
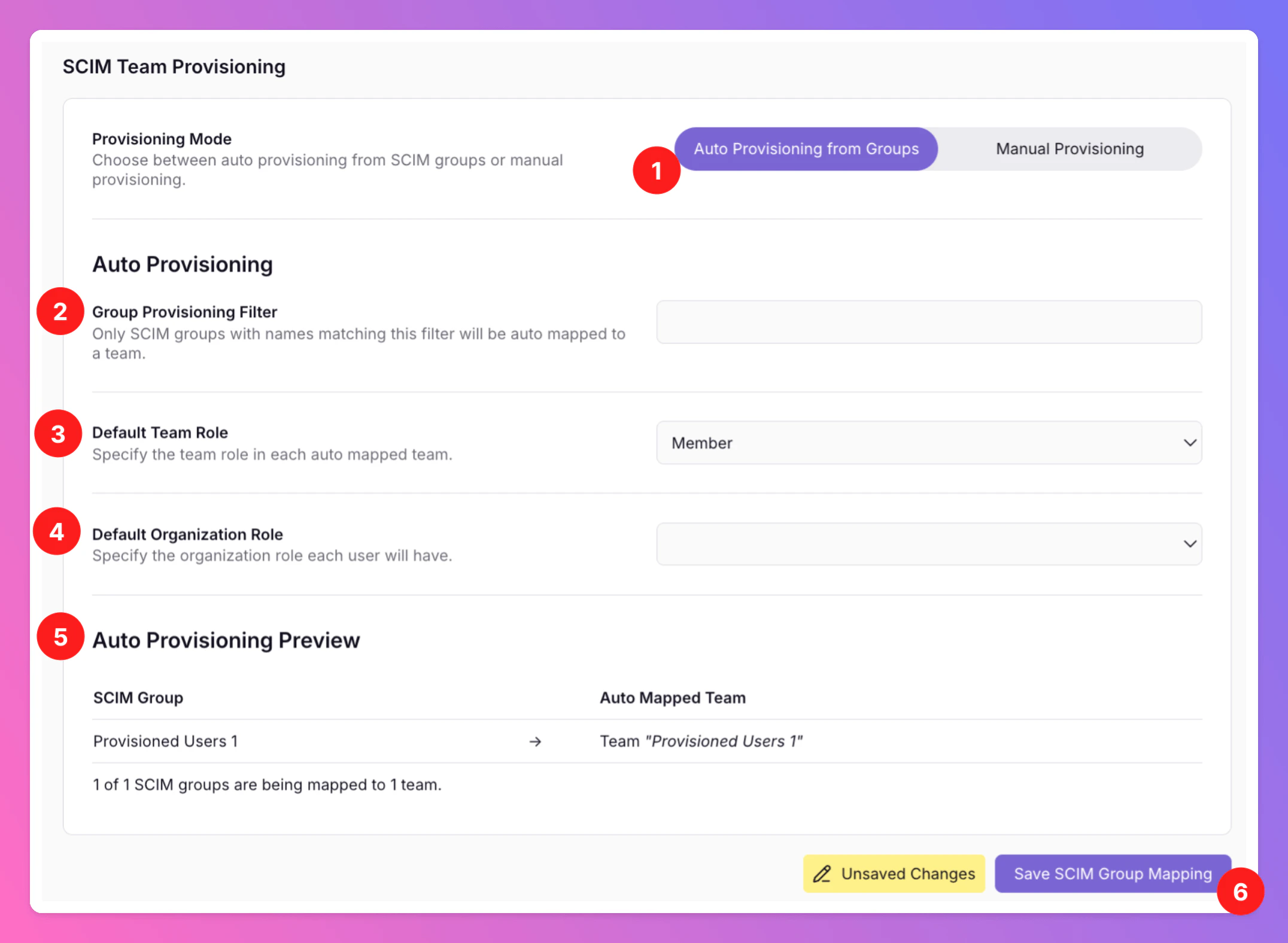
- In this case, we’ve selected Auto Provisioning from Groups as provisioning mode. For this mode you don’t have to create All Quiet teams in advance. However, it’s also much stiffer.
- Auto Provisioning options include a Group Provisioning Filter: You can use this field if you only want certain SCIM User Groups to be auto provisioned to All Quiet Teams.
- Default Team Role: Choose whether provisioned users should be assigned Member or Administrator roles within the Teams.
- Default Organization Role: You can additionally assign Member,Administrator or Owner roles within the Organization.
- A preview showing which SCIM User Groups will create which All Quiet Teams.
- Again, safe to create the teams and roles through auto provisioning mode.
Provisioned Users Cannot Be Edited via Web App.
To ensure that the resources managed via your SCIM provider stay in sync with your setup, we lock provisioned resources within the Web App. This means these resources cannot be edited or deleted directly through the Web App’s interface. Provisioned resources are marked with an icon, and hovering over it will display a message explaining why the resource is locked and cannot be modified via the Web App.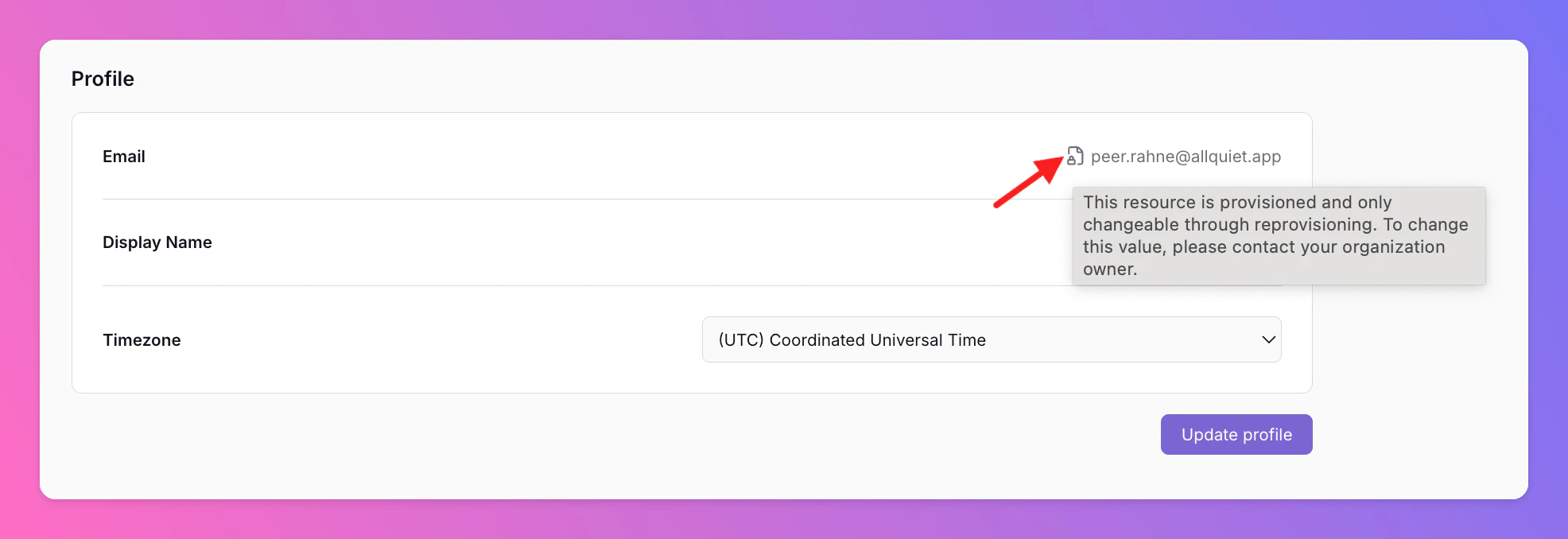
SSO page of your organization. If you want to change your settings, please contact support@allquiet.app.